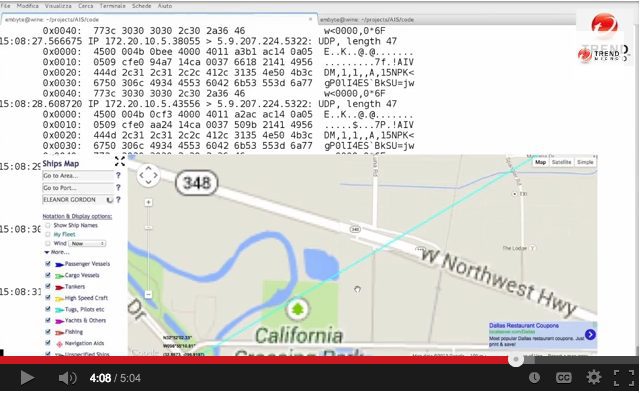
The researchers at Trend Micro have exposed some significant vulnerabilities to the security of the Automatic Identification System (AIS), a ship identification system relied upon by mariners, VTS operators, government agencies, and likely enemies to all of the above to identify and track vessels.
As the above video shows, tampering with AIS data is quite feasible. Trend Micro notes that the following modifications are possible:
- Modification of all ship details such as position, course, cargo, flagged country, speed, name, MMSI (Mobile Maritime Service Identity) status etc.
- Creation of fake vessels with all the same details e.g. having an Iranian vessel with nuclear cargo show up off the coast of the United States
- Create and modify Aid to Navigations (AToN) entries, such as buoys and lighthouses. This leads to scenarios such as blocking the entrance to a harbor, causing a ship to wreck, etc.
- Create and modify search and rescue marine aircraft such as helicopters, and light aircraft e.g. having a stationary search and rescue coast guard helicopter “take off” and travel on a set course.
- Impersonate marine authorities to permanently disable the AIS system on a vessel, both forcing the ship to stop communicating its position, and stop getting AIS notifications from all nearby vessels (essentially a denial of service attack). This can also be tagged to a geographical area e.g. as soon as ship enters Somalia sea space it vanishes of AIS, but the pirates who carried out the attack can still see it.
- Fake a “man-in-the-water” distress beacon at any location that will also trigger alarms on all vessel within approximately 50 km.
For more information on AIS vulnerabilities found by Trend Micro, visit their blog HERE.
Editorial Standards · Corrections · About gCaptain

 Join The Club
Join The Club